Introduction This document answers frequently asked questions about Cisco's VPN Client solutions available on Mac OS X. The contents of this document have been moved, you should be able to find them here: VPN Clients For Mac OS X FAQ - Cisco Systems. Runs on: Mac OS X 10.2, Mac OS X 10.3, Mac OS X 10.4, Mac OS X 10.5 DVD to iPod Converter for Mac Platinum v.4.5.23 iBestsoft DVD to iPod converter is a specially designed for Mac Powerpc or Intel users to convert DVD to iPod video and convert DVD audio to.
All three VPN types (SSL VPN, IKEv2 VPN, and Clientless SSL VPN) are available for Mac OS X 10.9 (Mavericks) and higher. The following instructions will help you create and use the VPN option of your choice. For more information on the VPN types, see VPN.
- 1Using the SSL VPN Option on Mac OS X
- 2Using the IKEv2 VPN Option on Mac OS X
Using the SSL VPN Option on Mac OS X
This option works best on Mac OS X versions below 10.11 (El Capitan).
Setup the CAEDM SSL VPN on Mac OS X
- Using your web browser, go to https://vpn.et.byu.edu
- NOTE: If you get an orange login screen, then you have entered the wrong address and you will not be able to login. Try again with the exact address listed above.
- In the blue Please login box, enter your username and password
- Click Login
- In the FortiClient Download box, click FortiClient Mac
- NOTE: You can alternatively download the FortiClient for Mac from https://www.forticlient.com.
- Run the client installer you just downloaded. The install process will:
- Unpack the installer
- Run a virus scan
- Present you will a license agreement, which you will have to accept to continue
- Prompt for Complete or VPN only install; choose the VPN Only button
- Prompt for an install location; accept the default
- Prompt to confirm your previous settings and continue the install
- Install the client
- NOTE: The installer will create a new 'fortissl' adapter in your list of network connections. Do not change or remove the fortissl adapter, or the SSL VPN will not work
- Prompt to finish the install; Click Finish
- Open the FortiClient either from the Spotlight, or from the FortiClient icon in the menu bar.
- Click Configure VPN
- Click the SSL-VPN button at the top, if it is not already selected
- In the Connection Name field, enter
CAEDM SSL VPN - In Remote Gateway, type in
vpn.et.byu.edu - Click Apply, and then click Close
To connect to the CAEDM SSL VPN
- Open the FortiClient application, either from your menu bar if FortiClient was automatically started, or from the Spotlight
- Select the CAEDM SSL VPN connection, if it is not already selected
- Enter your Username and Password in the appropriate fields
- Click Connect
To disconnect from the CAEDM SSL VPN
- Click on the FortiClient icon on your task bar.
- Click Disconnect.
Using the IKEv2 VPN Option on Mac OS X
Setup the CAEDM IKEv2 VPN on MacOS (above 10.11)
Beginning with MacOS 10.11 (El Capitan), Apple has provided IKEv2 VPN support built-in to MacOS. The following instructions were based on MacOS 10.13 (High Sierra), but should be similar for 10.11 (El Capitan) and 10.12 (Sierra).
Screenshots are available after the instructions (click to view full size).
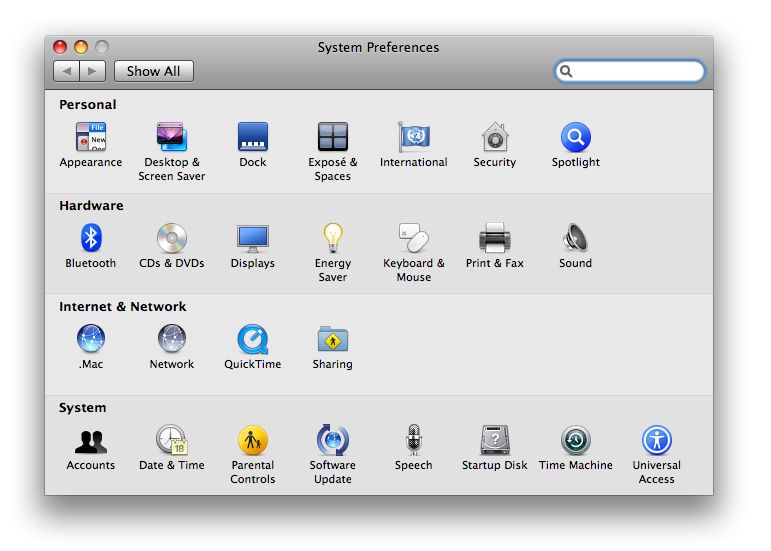
- Open System Preferences, and click on Network. Click the plus icon in the bottom left of the Network Preferences window.
- Select VPN under Interface.
- Select IKEv2 under VPN Type.
- Type a description for the VPN in the Service Name box (for example, CAEDM IKEv2 VPN).
- Click create.
- Enter vpn.et.byu.edu for Server Address and Remote ID.
- Click Authentication Settings.
- Select Username in the drop-down menu.
- Type your CAEDM username and password in their respective text boxes.
- Click OK.
- Click Connect.
At this point, you should be successfully connected to the CAEDM VPN!
Setup the CAEDM IKEv2 VPN on Mac OS X (below 10.11)
Apple has yet to release official IKEv2 support for Mac OS X. While the strongSwan IKEv2 client works, you must change your Network Location each time you connect or disconnect with the VPN. Otherwise OS X will ignore settings provided by the VPN, and be unable to find other computers. For this reason, the SSL VPN client is easier to use when using a Mac. If the SSL VPN does not work for you, or if you would still like to use the IKEv2 VPN instead, the instructions are as follows:
NOTE: The following instructions are based on OS X 10.9 (Mavericks) and 10.10 (Yosemite). Other versions of OS X may vary.
- Download the strongSwan client zip file from http://download.strongswan.org/osx/strongswan-5.3.0-1.app.zip
- Double click the strongswan-5.3.0-1.app.zip file you just downloaded. This will extract the archive in the current folder
- Drag the strongSwan application to your Applications folder
- Double click the strongSwan application
- Confirm that you want to open an application downloaded from the Internet by clicking Open
- NOTE: You will now have a light-gray swan icon in your menu bar. This will be the only indication strongSwan is running.
- Click on the light-gray strongSwan icon in the menu bar, and click Add Connection...
- In the Connection name field, enter
CAEDM IKEv2 VPN - In the Authentication selector, choose IKEv2 EAP
- In the Server address field, enter
vpn.et.byu.edu - In the Username field, enter your CAEDM username
- Open up the System Preferences application
- Select Network
- Unlock the settings by clicking on the padlock icon on the left side
- In the Authenticate dialog, enter your password for your computer, and click Unlock
- In the Location field, select Edit Locations
- Click the + button, and in the new entry type
CAEDM IKEv2 VPN Location - Click Done. The Location field should now say CAEDM IKEv2 VPN Location
- Click the Advanced... button at the bottom of the Network settings window
- Click the DNS tab
- Under the DNS Servers box, click the + button
- In the new entry, type
128.187.48.2 - Under the DNS Servers box, click the + button again
- In the new entry, type
128.187.56.2 - Click OK
- Click Apply at the bottom of the Network window
- Close the Network window by clicking on the red dot in the upper left corner
- Click the Apple icon in the menu bar
- Point to Location, and click Automatic
To connect to the CAEDM IKEv2 VPN
- Start the strongSwan app from the Spotlight (if it isn't already running)
- Click on the light-gray strongSwan icon in the menu bar
- Point to CAEDM IKEv2 VPN, and click on Connect
- In the Password required dialog that pops up, enter your CAEDM password, and click OK
- NOTE: When the light-gray strongSwan icon in the menu bar changes to black, you are connected to the VPN. But, you must change the Network Location, or you will be unable to connect to other computers.
- Click the Apple icon in the menu bar
- Point to Location, and click CAEDM IKEv2 VPN Location
You are now connected to the CAEDM IKEv2 VPN.
To disconnect from the CAEDM IKEv2 VPN
- Click on the strongSwan icon in the menu bar
- Point to CAEDM IKEv2 VPN, and click Disconnect
- NOTE: When the black strongSwan icon in the menu bar changes to light-gray, you are disconnect from the VPN. But you must change the Network Location back to Automatic, or you will be unable to connect to other computers.
- Click the Apple icon in the menu bar
- Point to Location, and click Automatic
You are now disconnected from the CAEDM IKEv2 VPN
Confirmed working on OS X High Sierra
The proprietary CiscoVPN Mac client is somewhat buggy. It is possible to use the IPSec VPN software included with Mac OS X instead. This tutorial shows you how to migrate from CiscoVPNto the native OS X IPSec VPN by decrypting passwords saved in CiscoVPN PCF files.
Please visit these guys if their offer interests you - they make this site possible.
Open up your System Prefrences and select 'Network'. Click on the little + button at the bottom of the window to create a new connection.
Pick 'VPN' for the Interface and set its type to 'Cisco IPSec'. It doesn't matter what you set as the service name.
Copy the 'Host' setting from CiscoVPN...
to the 'Server Address' setting in your System Prefrences' and enter your username under 'Account Name'. You probably don't want to enter your passwordunless you are OK with the system saving it.
On Mac OS X, PCF files are usually found in /private/etc/CiscoSystemsVPNClient/Profiles. Open up /Applications/Terminal and type the following:
You should get something like this:
Find that long list of letters and numbers after enc_GroupPwd= and copy it. Also make note of the GroupName - you'll need that in a bit as well.
Paste that sequence of characters into the fancy schmancy decoder ring below and click 'Decode'. (pops up a new window)
Fancy Schmancy Decoder Ring
As an example, this should return 'letmein' as the password:
Thanks to HAL-9000 at evilscientists.de and Massar's work on cisco-decrypt.c for the magic here. A JavaScript implementation also exists here: https://github.com/artemkin/cisco-password-decoder.
Click 'Authentication Settings' back in the Network Prefrences screen. Enter the resulting decoded password into the 'Shared Secret' section of the new VPN connection and set the GroupName from above as well.
Click 'OK', make sure 'Show VPN status in menu bar' is checked and click 'Apply'.
At the top of your screen you should have a little VPN icon. Try connecting to your new VPN.
If everything goes as planned, you should see your connection time counting up at the top of your screen.
How to get your VPN settings out of the built-in mac VPN client.

You don't need the Fancy Schmancy Decoder Ring to get your settings back out of the built-inMac VPN client. Just head over to the Keychain Access application (under Applications -> Utilities) and search for 'VPN'. Double-click your IPSec Shared Secret to open up the window. Clicking 'Show Password' will reveal the secret sauce after you authenticate.
If things seem to get hung-up and you are unable to reconnect your VPN without a reboot, Rick R mentions that you might try killing the 'racoon' process.
Racoon is an IPsec key management daemon and is part of the KAME IPsec tools. Kill it by running 'Activity Monitor' in the 'Utilities' folder, finding it in the process list and clicking 'Quit Process' at the upper left of the Activity Monitor window.
Look in your system.log by running the Console app for hints at what might be going wrong. Here's the system.log from aworking VPN setup / take down.
Disconnects
Dave Ma's VPN would disconnect after 45 minutes of uptime. Fotos Georgiadis on an Apple forum threadsuggested changing the IPSec proposal lifetime within racoon to 24 hours instead of 3600 seconds.(3600 seconds is 1 hour - who knows why people are seeing drops at 45 minutes)Here's how that is done.
Connect to the VPN (so OSX dynamically generates a racoon configuration file)
Open Terminal on Mac (Applications --> Utilities--> Terminal)
Copy the generated configuration file to /etc/racoon:
sudo cp /var/run/racoon/XXXXXX.conf /etc/racoon**where: XXXXXX is the name or ip address of your VPN server**
Edit the racoon configuration file with your favorite editor (pico):
sudo pico /etc/racoon/racoon.confAt the bottom of the racoon.conf file, comment out the line:
# include '/var/run/racoon/*.conf';(by added the '#' to the beginning of the line)
And instead include the copied file (which we will edit):
include '/etc/racoon/XXXXXX.conf';(don't forget to replace XXXXXX with the actual name of your file)
Edit the generated configuration file with your favorite editor (pico):
sudo pico /etc/racoon/XXXXXX.confDisable dead peer detection:
dpd_delay 0;Change proposal check to claim from obey:
proposal_check claim;Change the proposed lifetime in each proposal (24 hours instead of 3600 seconds):
lifetime time 24 hours;*note: make sure you change all the 'proposed lifetime' sections and not just one.
Disconnect and reconnect (this time racoon will use your custom configuration).
Now try using your VPN for more than 45 minutes and it shouldn't drop.
So does all your traffic flow through the VPN when you are connected or just traffic to the protected networks? Cisco VPN servers normally send out a list of routes to private networks so you don't end up sending all of your traffic through the VPN server. The reasoning behind this is why protect it if the traffic is destined for an insecure network anyway? The native OS X Cisco VPN adds these routes automatically and removes them when you disconnect. That's one of the things that differentiates the Cisco VPN client from the standard IPSec client. Let's take a look at what gateway is used when sending traffic to apple.com from within the Terminal application:
Notice the 'gateway' line there? Traffic to apple.com is going out 192.168.1.1 which is my normal Internet gatewayso it is skipping the VPN entirely.
Let's try an IP on a protected private network: (10.1.2.3)
In this case, the gateway is 172.131.25.12 which is a fake IP on the far end of the VPN which will eventually route traffic to 10.1.2.3. So when sending data to 10.1.2.3, I am going through the VPN and that traffic is encrypted.
So how does it know what gateway to use for different IPs? Let's take a look at the routing table:
I've lopped off a bunch of irrelevant lines but as you can see we have two 'default' routes. If a destination isn'texplicitly matched below, the traffic will flow through the first default route from the top. So in this case, ifthe destination isn't within 10.1/16 (which means 10.1.*.*) we will go through our default route of 192.168.1.1. Ifit is, we would go through 172.131.25.12 which is our VPN.
But what if you just wanted to send everything through your VPN connection? We could just delete the first default route and let everything go over the VPN, but this is presumably dangerous because the encrypted traffic probably uses the default route to get to the VPN server in the first place. Let's see:
Yep, it does. So if we are going to remove the default route to 192.168.1.1, we have to make sure we have an explicitroute below to the VPN server. (1.2.3.4) You will notice above that my Cisco VPN server adds this route automatically, but if yours isn't configured that way you can add it like this:
It is safe to try this if you already have the route because the command will just fail.
The next thing we are going to do is a little dangerous and remove all your network access. A reboot should be your weapon of last resort to get your networking back but you might also want to print these instructions out so you havethem. You have been warned!
Now let's do the dangerous bit and rip the first default route away:
Now let's check to see if we can still get to our VPN server:
Yep, looks good.
Now let's look at the wider Internet by seeing how we get to apple.com: (17.172.224.47 - we aren't using apple.com here because we don't want to depend on DNS working)
Whoops, something is wrong! That's because that first route there is a little deceptive. It isn't aroute to the IP of the gateway, just a route to the VPN tunnel device utun0. We'll need to say what IPto go to. Let's add a default route to the VPN's fakenet gateway address: (which we already have as the gateway in most other routes)
OK, let's see which way packets go to get to apple.com: (17.172.224.47)
Yep, looks like the right way.
Now let's try pinging google.com: (apple.com doesn't respond to pings)
Looks like it works. If it doesn't work, your VPN server likely doesn't allow general Internet access throughVPN connections. If this is the case, you are out of luck. Hopefully you know someone influential in the ITdepartment that can change this for you.
Because we removed the normal default route, when we shut down our VPN we'll be stuck without a default route.To add that back in after the VPN goes down, do this:
And we should be back to normal.
Ideally we do these things automatically when the VPN comes up. The easiest way to do this is to have yourVPN administrator set that up as a policy for you. Alternatively, you can create scripts that run on VPN startup.Create /etc/ppp/ip-up and add whatever lines you came up with above to that and mark that file as executablewith:
Similarly, /etc/ppp/ip-down will be run on VPN shutdown. Reverse your commands in that file and you shouldhave a completely automated setup.
Happy tunneling!
-Anders Brownworth
About Me:
Name:
Ssl Vpn For Mac Os X El Capitan
Anders BrownworthHome: Cambridge, MA, USA
Work: Mobile application and GSM research at Bandwidth.

Ssl Vpn For Mac Os X 10 11
Play: Technology, World Traveler and Helicopter PilotFollow: